Understanding Hidden Ransomware and Strategies to Detect It
Ransomware attacks are rife, with Norton estimating around 2,200 cyberattacks every day.
Verizon’s 2022 Data Breach Investigations Report shows that ransomware attacks surged 13% in 2022, a total higher than the past five years. In short order, ransomware attacks can destroy any business, which is why ransomware has become one of the most serious threats to global network security. To better understand this public enemy, we are releasing the anti-ransomware blog series.
Previously, in part 1 of this series, “The Ransomware Story: Predicting the Unpredictable“, we explored the concepts, history, and impact of ransomware. In today’s blog, we’ll look at what happens before a ransomware attack, and what we can do to prevent it.
The threats of ransomware

Ransomware differs from other cyber viruses in that it’s highly stealthy and destructive, and makes it difficult to recover data.
Stealthy
The camouflaged malware can gain access to a system through storage media, phishing emails, website Trojan horses, and zero-day vulnerabilities (security issues that are yet to be resolved), staying hidden for months before launching an attack. It encrypts the data and demands a ransom until it obtains higher privileges and holds large amounts of critical data.
Destructive
The company Cybersecurity Ventures estimates that in 2021, the global losses caused by ransomware attacks reached $20 billion, 61 times that of 2015. Ransomware not only causes losses from ransom, but also collateral damage such as downtime and a negative impact on brand image.
Difficult recovery
A ransomware attack can encrypt or delete data copies in both local and disaster recovery (DR) centers, affecting recovery efforts and causing data leaks. Sophos reports that it takes an average of 16 days to recover data, while the average cost of recovering from a ransomware attack was $1.85 million in 2021, up from $761,000 in 2020.
The background to an attack
To better defend against ransomware, it is important to understand the process. Let’s take a look at how malicious actors analyze and hack into a system.
Detection
In the early stage, hackers collect information about the target’s IT system, departments, leaders, email addresses, phone numbers, and other information through public channels or internal members, before starting long-term preparation on the target.
Invasion
Using various common intrusion methods, hackers exploit system vulnerabilities to enter the system and implant the virus. This process includes social engineering methods to impersonate public or executive mailboxes, sending phishing emails, masking malicious scripts or programs as common files, with the aim of tricking victims into downloading and running the files. Other methods to access internal servers include bribery and coercion, or other media such as USB flash drives and Wi-Fi networks that can implant ransomware into the system.
Defend against extortion attacks
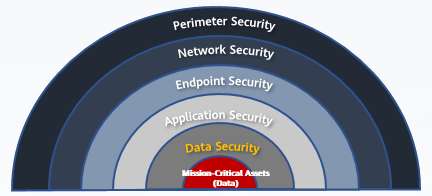
In Northrop Grumman’s Defense in Depth (DiD) model, there are five lines of defense against ransomware attacks.
Perimeter and network security measures are built into the network to detect and prevent and block known malware threats. Endpoint and application security are deployed at the host layer, to update system and software patches, making it harder for cybercriminals to exploit vulnerabilities. Both network- and host-layer measures are passive forms of defense, meaning that firewalls and antivirus software can only prevent attacks from known viruses.
At this point, if the first four layers of defense have failed, the victim will likely be held to ransom. As the last line of defense, storage systems must be proactive in the fifth and final layer of defense.
Huawei Ransomware Protection Storage Solution: The Cutthroat Detector

While ransomware attacks may be unavoidable, we can at least mitigate the damage. Storage should immediately detect abnormal I/Os and quickly start data protection to reduce losses. Huawei storage can identify 99.9% of ransomware threats, and thanks to machine learning models, can analyze both production and backup copies. By comparing the metadata of snapshot copies and using the AI model to determine whether files are encrypted, the Huawei storage solution can ensure that data is not tampered with, and safe to use.
Storage serves as the last line of defense for data security, helping protect data with pre-attack defense, during-attack blocking, and post-attack recovery. With the industry’s most comprehensive ransomware protection solution, Huawei is empowering organizations to say “no” to extortion.
Visit the product page Huawei Ransomware Protection Storage Solution and stay tuned for part 3 of this series: “Understanding the Stages and Response to a Ransomware Attack.”
Disclaimer: Any views and/or opinions expressed in this post by individual authors or contributors are their personal views and/or opinions and do not necessarily reflect the views and/or opinions of Huawei Technologies.
Leave a Comment